Summary of Lecture 2
Binary relation: from to ,
Equivalence relation: a binary relation on a set .
- reflexive:
- symmetric:
- transitive:
- equivalence class
Congruence:
❌
✅
- or (iff )
s.t.
Arithmetic operations over the set
partition
- //not an equality of sets
has an inverse
DEFINITION: Let and . The residue class is called an inverse of if .
- The inverse of a residue class is unique (if exist). We denote .
- division: If , define
THEOREM: Let . has an inverse if and only if .
- Only if: such that ;
;
- If: such that
DEFINITION: Let . Define .
- If is prime, then
- If is composite, then
EXAMPLE:
Euler’s Phi Function
QUESTION: How many elements are there in
is the number of integers such that
DEFINITION (Euler’s Phi Function) .
- is the number of integers such that
//notation: - Gauss chose the symbol for Euler’s Phi function
THEOREM: Let be a prime. Then .
- Let .
- iff
iff
EXAMPLE:
EXAMPLE:
QUESTION: What is the formula of for a general integer ?
THEOREM: If for distinct primes and integers , then . Hence, .
- There are many proofs. We will see in the future.
- Principle of inclusion-exclusion
- Chinese remainder theorem
COROLLARY: If for two primes , then .
EXAMPLE:
Euler’s Theorem
THEOREM (Euler, 1760) Let and . Then
- are both residue classes modulo
- Suppose that for . Then is
- How to prove?
- Consider the map
- We show that is injective
- , this is because
- Suppose that
- , this is because
- , i. e.,
Equivalent form: Let . Then for any integer a such that
Fermat’s Little Theorem
EXAMPLE: Understand Euler’s theorem with .
- ,
- Consider the map
- ;
;
,
- is injective
Fermat’s Little Theorem (Euler, 1736) If is a prime and .Then .
- By Euler’s theorem,
Equivalent form: If is a prime, then for any integer .
Cryptography
- Confidentiality: The property that sensitive information is not disclosed to unauthorized individuals, entities, or processes.
–FIPS 140-2
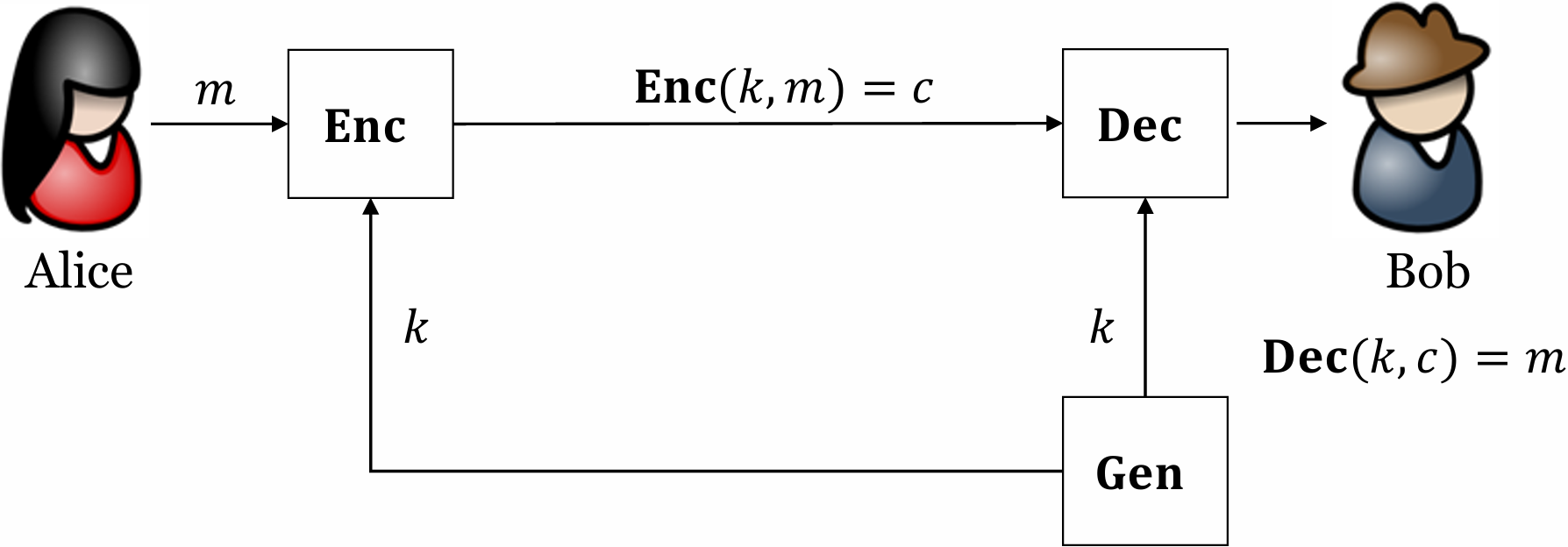
Private-Key Encryption
- : key generation, encryption, decryption
- : plaintext (message), ciphertext, secret key
- : plaintext space, ciphertext space
- Correctness: for any
- Security: if is not known, it’s difficult to learn from
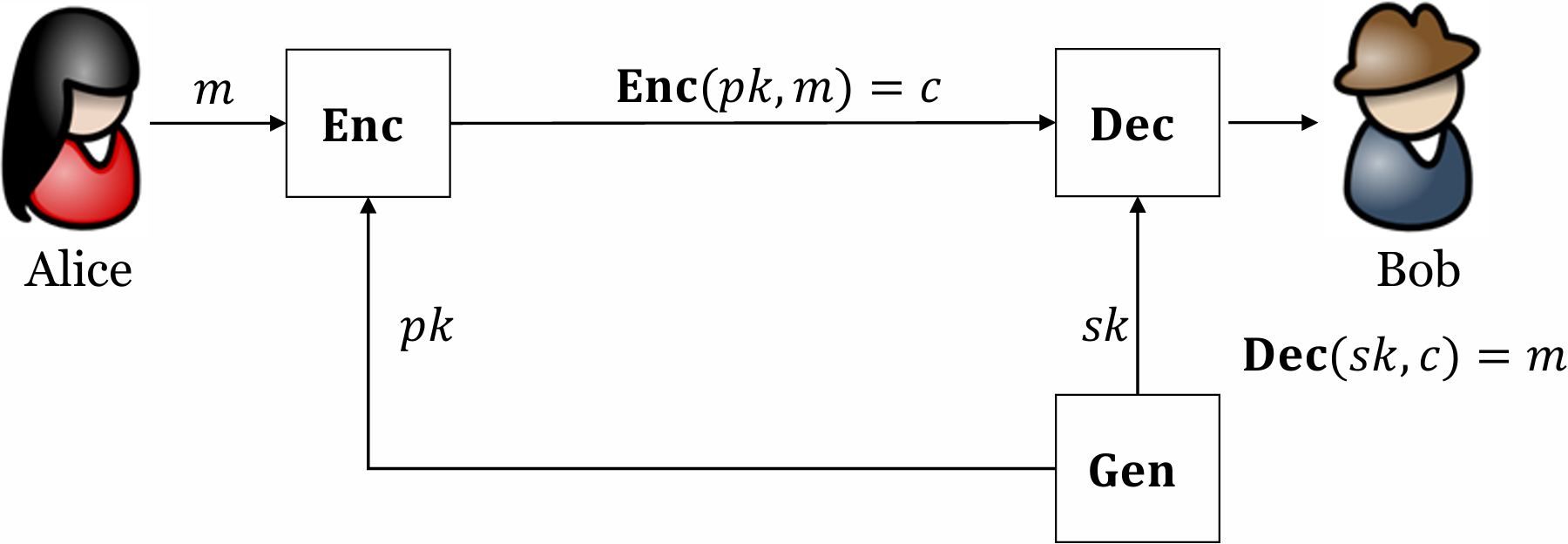
Public-Key Encryption
- : key generation, encryption, decryption
- : plaintext (message), ciphertext, public key, private key
- : plaintext space, ciphertext space
- Correctness: for any
- Security: if is not known, it’s difficult to learn from
RSA
CONSTRUCTION: , the message space is
- choose two -bit primes
- choose s.t. ,
- output
- :
- output
- :
- output
?
- s.t.
RSA is correct!
1977, Rivest, Shamir and Adleman: A method for obtaining digital signatures and public-key cryptosystems. MIT/LCS/TM-82. (Turing Award 2002)

讲义里ℤₙ*的定义写得有点绕,其实不就是和n互质的数嘛。
有人试过用小素数手算整个RSA流程吗?想验证下理解对没。
太浮躁了根本静不下心推公式,唉。
费马小定理原来是欧拉定理的特例,懂了
我也是刚反应过来
ed=1+tφ(N)这步是关键
RSA核心公式
这模运算得多练两遍才能搞明白。
模运算确实需要多练
选大素数p和q才是最难的吧?
ϕ(pq)=(p-1)(q-1)这步妙啊
我也觉得,这步太绝了
RSA 背后全是数论,太硬核了
我也觉得超硬核
费马小定理是欧拉定理的特例吧?
没错,n是质数时就是它
欧拉定理那个证明绕得我头晕,但例子一算就通了。
看到 RSA 证明那段终于串起来了
终于串起来了太爽了
原来RSA里的d是这么算的,之前一直没搞懂
同感,我之前也卡在这里
欧拉定理证明那段挺妙的
同感,那段证明很精彩
模n下除法原来就是乘逆元,早说啊!
ϕ(12)到底是多少?算出来是4但总感觉不对🤔
之前搞RSA实验,卡在求d上,现在看懂了是模逆问题。
这讲义比我们老师上课还清楚,服了。
看完后我突然想起大学时的数论课,老师讲的欧拉定理配合例子,感觉这次复习把所有细节都串起来,真的很有成就感 😂
之前写过RSA实现,发现选p、q要防止太接近,否则安全性下降。
我想问下,选e时真的只能是质数吗?还是可以选其他互质的数?
e不一定要质数,只要和φ(n)互质就行,比如65537常用但不是必须。
这篇笔记把剩余类弄得清晰多了。
剩余类那块图要是能动起来就更好了。
好像又要去复习一下互质的概念。
算了,我的phi函数算错了,哭。
这段关于模逆的解释,我懂了。
RSA的密钥生成过程原来这么抽象。
密钥生成抽象?其实是把数学包装成步骤了,多推两遍就顺了。
感觉欧拉函数的公式挺好记的。
看着欧拉定理又想起高中数学,真是脑洞大开 😂
phi函数的通式里,p的幂次怎么处理?有人能举例说明吗?
这下终于把欧拉定理的证明串起来了。
同余运算这块应用还挺广的。
确实,很多领域都用得上。
同余类划分这块还是有点绕。
欧拉函数这公式看着就头大。
同感,看久了眼睛花。
RSA这加密方式有点意思。
确实挺巧妙的
欧拉定理的证明挺巧妙。
同感,证明很精炼
费马小定理原来可以这么用。
同感,感觉一下子打通了
这课笔记也太硬核了。
同感,看得头大。
同余类的运算规则看懵了。
欧拉函数这块有点绕
RSA加密原来是这样推导的。
这段欧拉定理讲得挺清晰。