Summary of Lecture 4
Security of RSA: Without , it’s difficult to learn from
- “Factoring is easy” “Plain RSA is not secure”
- “Plain RSA is secure” “Factoring is hard”
- “Factoring is hard” “Plain RSA is secure”? //not proved, likely true
Commitment Scheme:
- hiding:
- binding: and ? Impossible
CONSTRUCTION: based on RSA
- Com:
- Ver:
RSA Implementation:
- choose efficiently? compute efficiently? compute / efficiently?
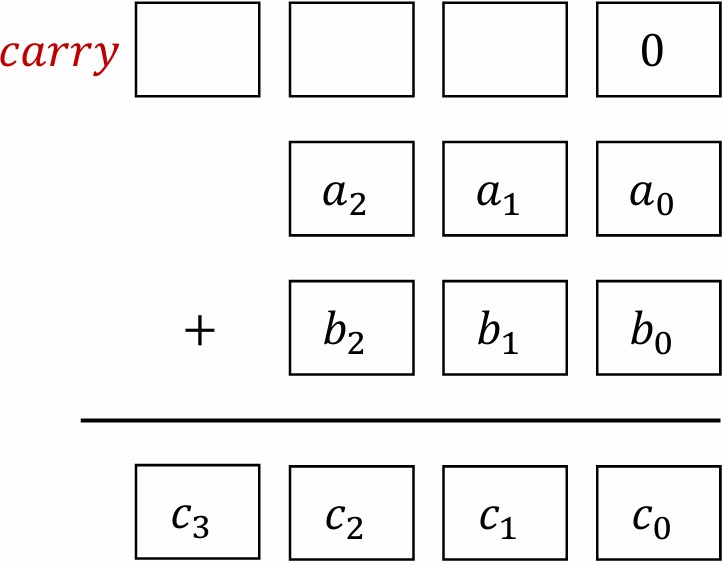
Addition
Binary Representation of an integer : a 0-1 sequence / binary string such that
Bit Length of Integer :
Algorithm for Addition:
- Input: //
- Output: //
- for to do
- //
- set and such that //
- Complexity: bit operations
Big O notation:
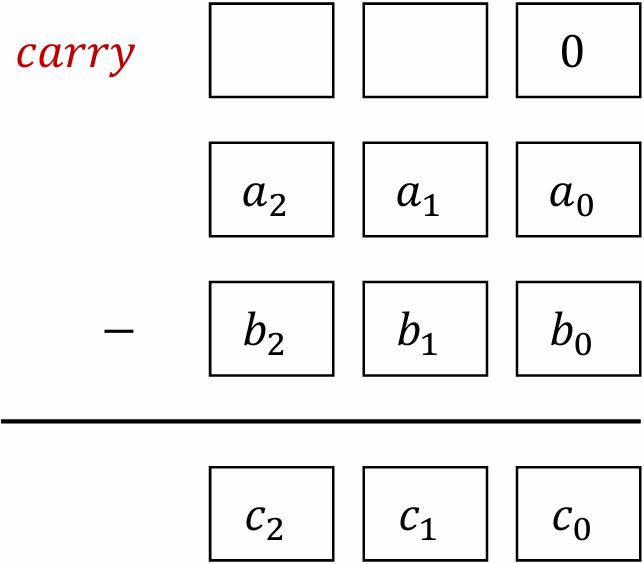
Subtraction
Algorithm for Subtraction:
- Input: //
- Output: //
- for to do
- //
- set and such that //
- Complexity: bit operations
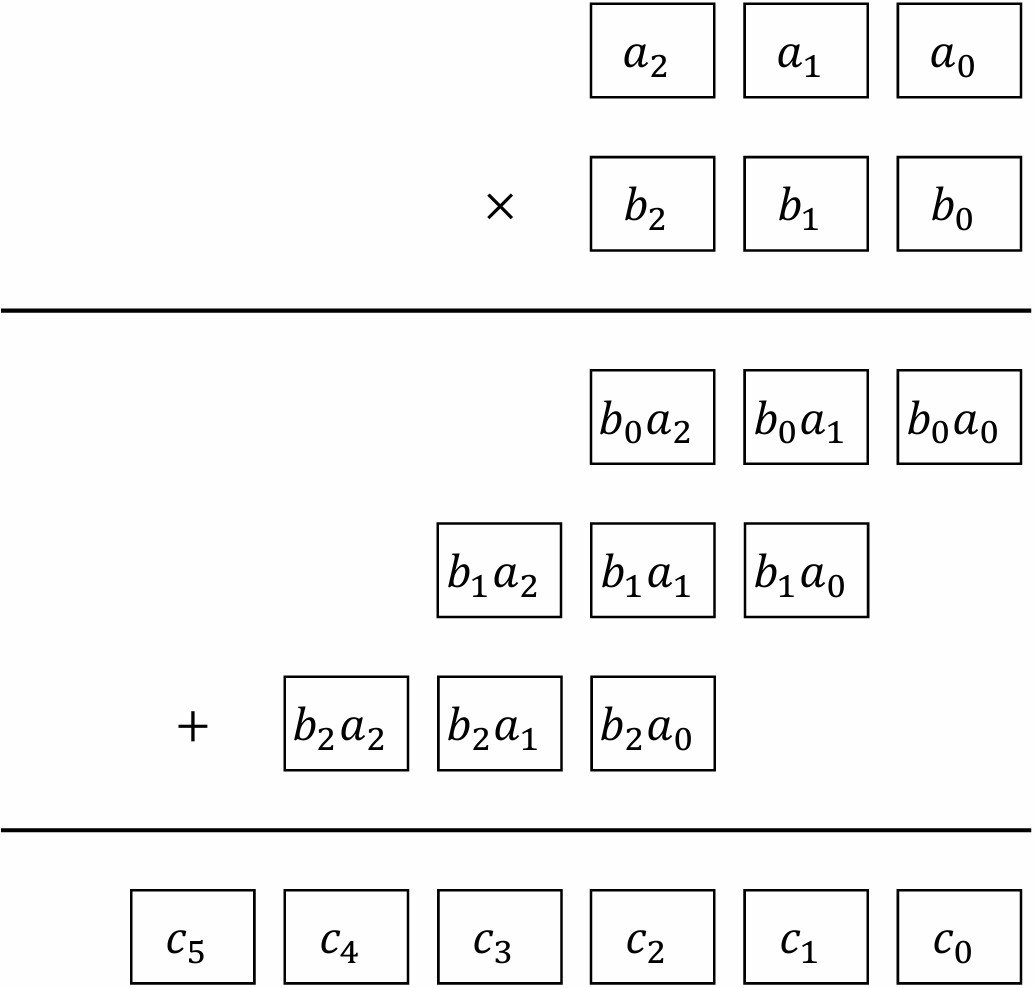
Multiplication
Algorithm for Multiplication:
- Input: //
- Output: //
- for to do
- if , then ;
- ;
- Complexity: bit operations
Division
Algorithm for Division:
- Input: //
- Output: and //
- for down to do
- //
- If , then // and
- while do
- output and
- Complexity: bit operations
Example:
Arithmetic Modulo
THEOREM: Let . Then
- can be computed in bit operations
- are computable in bit operations
- : computable in bit operations
- can be computed in bit operations
- is computable in bit operations
- : computable in bit operations.
Modulo exponentiation: For
- Complexity? How to compute efficiently?
EXAMPLE: modulo exponentiation
- 143733911392049898163790620742447116344546040644898141520376037626365007809899615665793895112104794373551079787727363529151277801402630305742433442340983358787394193855033926469913603762712163723160462115649025
- 46310011625494823943446873944318243690297367227688331207962573871391818800156614404181253994785434292576255362553884181998492463297303466464428022018327564723810228367576715525319623371983456905064392494176785
- 245246644900278211976517663573088018467026787678332759743414451715061600830038587216952208399332071549103626827191679864079776723243005600592035631246561218465817904100131859299619933817012149335034875870551067
- 245246644900278211976517663573088018467026787678332759743414451715061600830038587216952208399332071549102628322861627039184220494270313938703906283392288487724394251766892786817697178343799758481228648091667216
- Complexity: multiplications modulo
- ?
–very slow
Square-and-Multiply
ALGORITHM: (200 BC) compute in polynomial time
- Input:; //
- Output:
- Square: this step requires multiplications modulo
- Multiply: this step requires multiplications modulo
- Complexity: multiplications modulo
–fast
EXAMPLE: Compute using square-and-multiply.
- Input:
- Square: multiplications modulo will be done
- Multiply: at most multiplications modulo will be done
Time-Lock Puzzle
Question: The fastest method of computing ? Square-and-multiply?
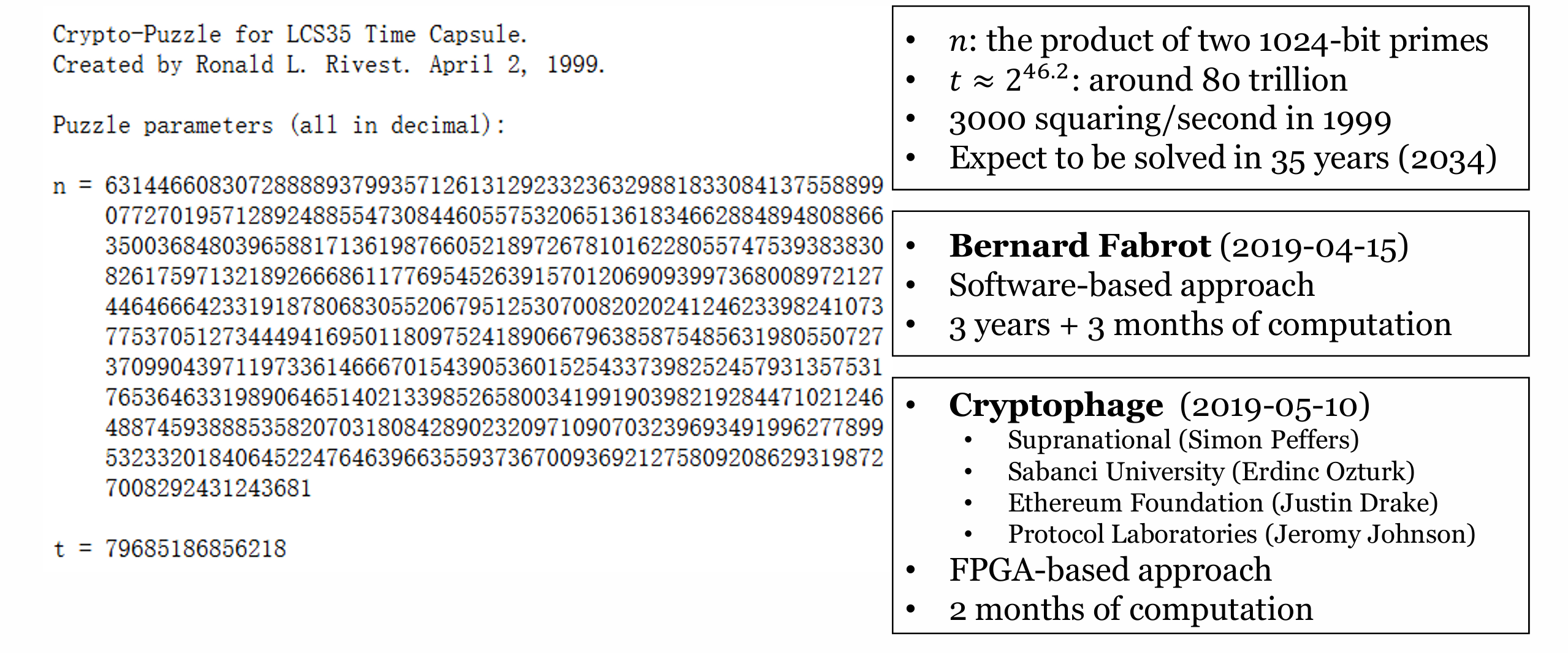
MIT LCS35 Time Capsule Crypto Puzzle:
- LCS 35th Celebration (April 12-13, 1999)
- By Ronald L. Rivest, Adi Shamir, and David A. Wagner
- Intrinsically Sequential Computations: Can’t be sped up using parallelism
- Creating the Puzzle:
- Create as the product of two primes
- Choose as the number of operations required
- Publish as the puzzle description
- Puzzle: compute
- Method: square-and-multiply (repeated squaring)
- Solution is
New puzzle: 2019-05-14 Expected to be solved in 2034
Modern applications: blockchain (green consensus)
Encrypting to the future
Question: Encrypt a message such that it can be decrypted (w/o key) in 35 years?
Encrypting a message to the future with TLP:
- Create a TLP with the aforementioned scheme. Record the primes .
- Compute quickly with the primes
- // is much smaller that
- Compute very quickly
- // Rivest, Shamir, Wagner, 1996
Analysis:
- With , it is very quick to compute and decrypt to
- With , it may take 35 years to compute and then learn
- Although Bernard Fabrot solved this with 3.5 years of computation
时间锁谜题这思路绝了,等于把计算难度当密钥用
区块链用这个做绿色共识,挺巧妙的
3.5年就解开了,本来要35年,这也太离谱了
这么快的吗
感觉平方乘算法比直接硬算快多了,这就是算法的魅力吧
mod N的运算复杂度原来只跟位数有关
那个LCS35谜题被破解是因为因数分解有突破吗?
平方乘算法在手算大数时候太好用了
手算神器,省得开电脑了
这算法公元前就有了?
古代算法现在还在用
给未来发消息这设定绝了,可惜得等这么久。
这排版公式太多,看着眼晕
那个时间锁谜题居然真有人跑了3.5年?也是够闲的
模指数运算这块儿看着就头大。
同感,每次看到都头疼
大数运算这块还是直接调库省事,自己写太容易出bug
大数幂取模这块儿有点绕。
同感,这块确实得花点时间理解。
平方乘算法用在区块链上还挺有意思的
区块链应用确实值得探讨
之前搞密码学作业就在这步卡壳,反复平方再乘确实比硬算快太多。
所以现在时间锁谜题还值得研究吗?
看到模运算就想起被期末考试支配的恐惧😂
期末考这玩意儿的时候差点挂科,现在看到还有阴影
手算验证了下除法算法,那个while循环确实需要小心处理
binding性依赖大数分解难度,目前还算安全
时间锁被提前破解说明硬件发展超预期啊
实际写代码时模幂运算边界处理挺折磨人的
量子计算机威胁是有,但现有密码体系没那么容易崩
这文章排版太密了,看得眼睛疼😵